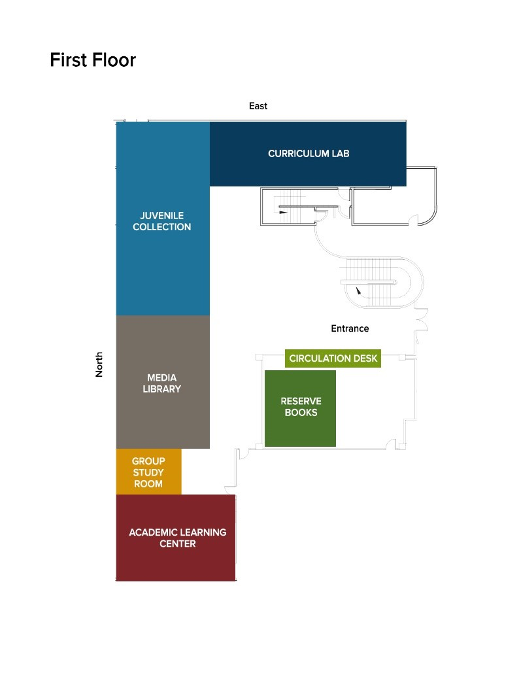
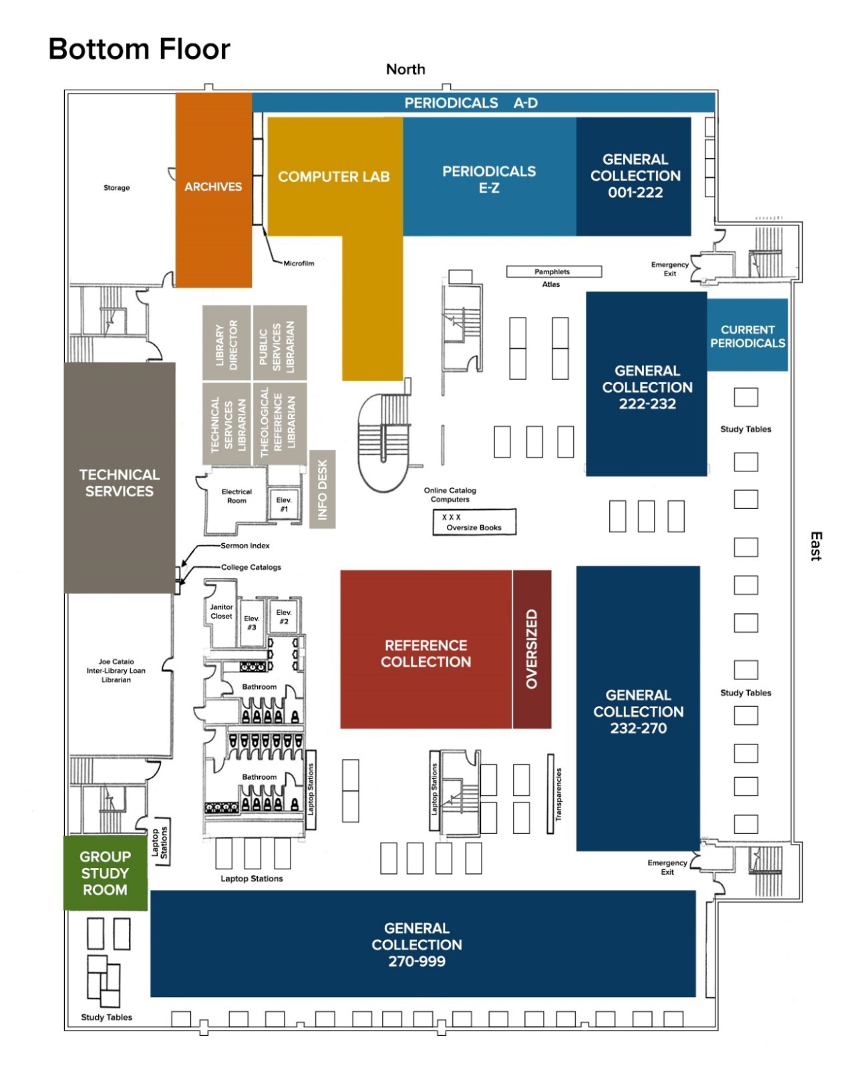
Crowell Library Maps
Crowell Library Equipment
Accu-Cut Machine
Computers
KIC Bookeye 4
Copy Machine
Microform and Microfiche
Student Lounge Amenities
Appropriate Computer Use Policy
The purpose of this policy is to ensure the legal, moral, and ethical use of the electronic resources* in Moody Bible Institute’s libraries. The Computer Use Policy must be read and agreed to by anyone wanting to use electronic resources in the library.
Use of these resources is a privilege and not a right. Users of these resources must abide by the guidelines in this document, all existing federal and state laws (including those regarding computer resources), and current copyright laws. Failure to comply with these regulations may result in suspension of privileges.
Users are expected to obey all posted signs, library staff instructions, and the contents of all library policies.
Users are prohibited from:
- Using library computers or the Moody network to impair the operations of computers, terminals, peripherals, or networks (i.e., introducing computer viruses, Trojan horses, worms, etc.)
- Using library computers to commit crimes and other unethical acts including illegally hacking websites
- Doing anything that will impair the operations of computers, terminals, peripherals, or networks
- Running or installing a program that could result in the eventual damage to a file or computer system, and/or the reproduction of itself, such as computer viruses, Trojan horses, and worms
- Violating copyright laws and software licensing agreements
- Sending or storing fraudulent, harassing, or slanderous email. Email may not be used for advertising, sending unsolicited messages or bulk messages (spamming), or sending or receiving obscene, pornographic, sexually explicit, or offensive material.
- Using the campus computers or network to access, store, or transfer objectionable or inappropriate material
- Material sent or viewed on the internet, email, file transfer, or any other electronic means that is inconsistent with these standards is not allowed.
Some examples of inappropriate content include, but are not limited to:
- Sexually explicit, suggestive, offensive, and obscene material
- Material that is harassing, slanderous, and intended to threaten individuals
- Material that may be used to cheat, plagiarize, or promote academic dishonesty
Information Systems, under the direction of the executive cabinet, reserves the right to limit access to certain areas of the internet that are of questionable nature and inconsistent with Moody’s values and community standards. All users will be responsible for information stored and retrieved on these computers.
Each visitor to a Moody Bible Institute library is responsible to abide by the above policies.
* Electronic resources include, but are not limited to, the internet, social media, email, discussion groups, and general computer usage.
